Securing Login Tokens in TuTiendaWeb
This post discusses improvements to login token handling within the TuTiendaWeb project.
The Challenge
Handling authentication tokens securely is crucial for any web application. A vulnerability in token generation, storage, or validation can expose user accounts and sensitive data.
The Fix
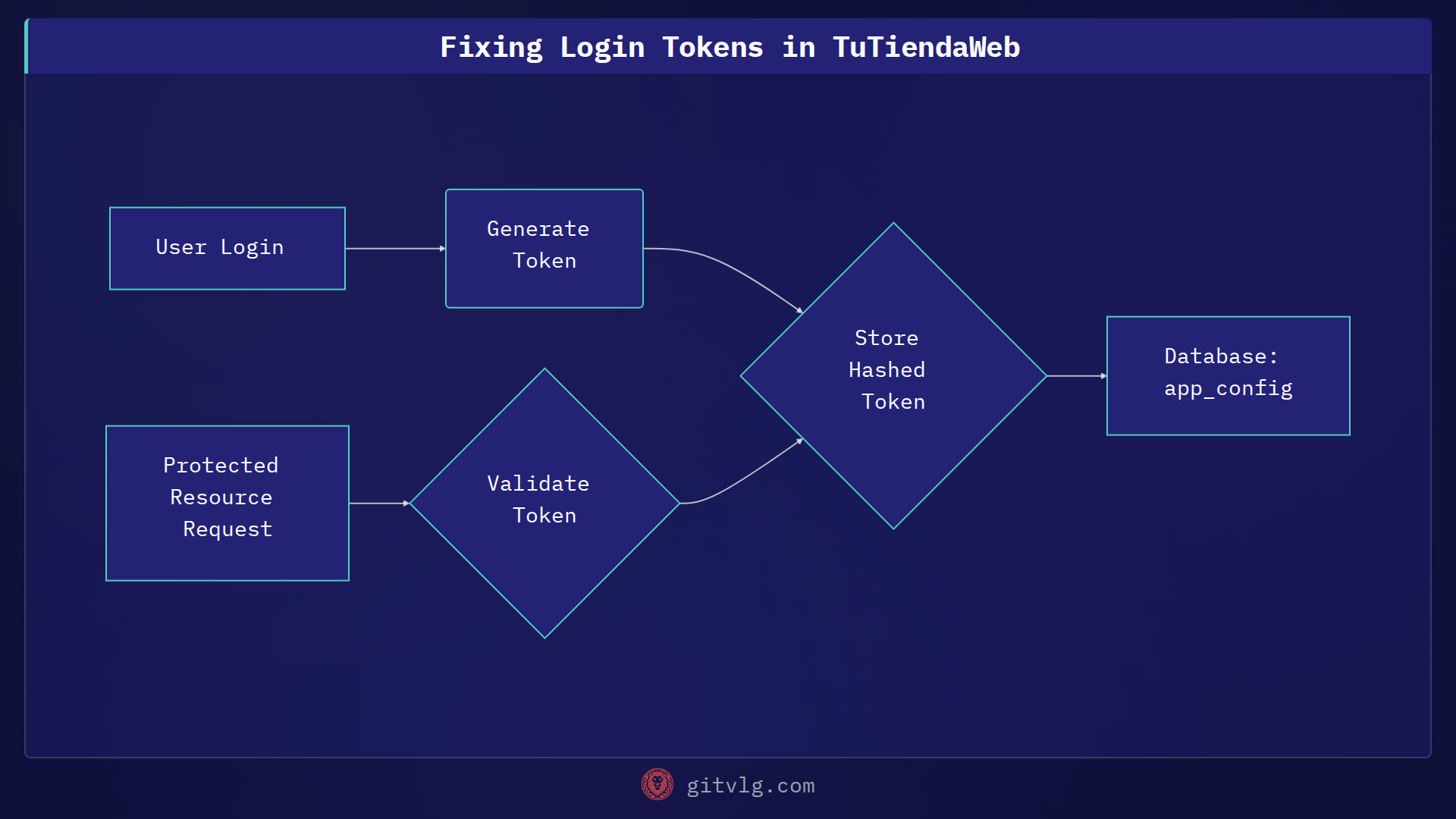
The recent changes focus on enhancing the security of login tokens. While specific implementation details are confidential, the general approach involves strengthening token generation and validation processes. This often includes:
- Improved Token Generation: Using stronger cryptographic algorithms to generate unpredictable and secure tokens.
- Secure Storage: Employing best practices for storing tokens, such as hashing and salting.
- Robust Validation: Implementing rigorous checks to ensure tokens are valid and haven't been tampered with.
Let's illustrate a common token validation pattern using TypeScript:
function validateToken(token: string): boolean {
if (!token) {
return false; // Token is missing
}
try {
// Placeholder for actual validation logic
// This could involve verifying the token's signature,
// checking its expiration, and ensuring it matches a stored token.
const isValid = token.length > 10; // Simplified example
return isValid;
} catch (error) {
console.error("Token validation error:", error);
return false; // Token is invalid
}
}
const userToken = "exampleToken123";
const isValid = validateToken(userToken);
if (isValid) {
console.log("Token is valid");
// Proceed with authentication
} else {
console.log("Token is invalid");
// Redirect to login
}
Best Practices for Token Security
Consider these general security measures when handling tokens:
- Use established libraries: Leverage well-vetted libraries for token generation and validation instead of creating custom solutions. Examples include libraries for JWT (JSON Web Tokens).
- Implement token expiration: Set appropriate expiration times for tokens to limit the window of opportunity for attackers.
- Rotate tokens: Regularly rotate tokens to minimize the impact of potential compromises.
- Store tokens securely: Avoid storing tokens in plain text. Use hashing and salting techniques to protect them.
- Validate tokens rigorously: Implement thorough validation checks to prevent unauthorized access.
The Takeaway
Prioritize login token security in your web applications. Strengthen token generation, storage, and validation processes to protect user accounts and data. Regularly review and update your authentication mechanisms to address evolving security threats.
Generated with Gitvlg.com